2026

Ano2Rule: Rule-Based Global Interpretation for Unsupervised Anomaly Detection in Security
Ruoyu Li *-, Yu Zhang *, Qing Li, Nengwu Wu, Yong Jiang, Weizhi Meng, Laizhong Cui (* equal contribution)
IEEE Transactions on Dependable and Secure Computing 2026 Received
Ano2Rule is a global interpretability method for unsupervised anomaly detection, which solves the opacity problem of black-box models through rule extraction. The method includes two core components: the internal clustering tree (IC-Tree) for decomposing complex data distributions into multiple sub-distributions, and the combined boundary exploration algorithm (CBE) for precisely inferring the decision boundaries of each sub-distribution. Experiments show that Ano2Rule has higher fidelity and robustness on real datasets such as network intrusion detection and Internet of Things security compared to baseline methods, while also supporting extended functions such as local interpretability and counterfactual explanations.
[IEEE Transactions on Dependable and Secure Computing] [PDF]
Ano2Rule: Rule-Based Global Interpretation for Unsupervised Anomaly Detection in Security
Ruoyu Li *-, Yu Zhang *, Qing Li, Nengwu Wu, Yong Jiang, Weizhi Meng, Laizhong Cui (* equal contribution)
IEEE Transactions on Dependable and Secure Computing 2026 Received
Ano2Rule is a global interpretability method for unsupervised anomaly detection, which solves the opacity problem of black-box models through rule extraction. The method includes two core components: the internal clustering tree (IC-Tree) for decomposing complex data distributions into multiple sub-distributions, and the combined boundary exploration algorithm (CBE) for precisely inferring the decision boundaries of each sub-distribution. Experiments show that Ano2Rule has higher fidelity and robustness on real datasets such as network intrusion detection and Internet of Things security compared to baseline methods, while also supporting extended functions such as local interpretability and counterfactual explanations.
[IEEE Transactions on Dependable and Secure Computing] [PDF]
2025

RM-PoT: Reformulating Mathematical Problems and Solving via Program of Thoughts
Yu Zhang, Changsong Lei
(arXiv) 2025 On Process
RM-PoT, a three-stage framework that integrates problem reformulation (RM), code-aided reasoning (PoT), and domain-aware few-shot learning to address these limitations. Our approach first reformulates the input problem into diverse surface forms to reduce structural bias, then retrieves five semantically aligned examples from a pre-constructed domain-specific question bank to provide contextual guidance, and finally generates executable Python code for precise computation.
RM-PoT: Reformulating Mathematical Problems and Solving via Program of Thoughts
Yu Zhang, Changsong Lei
(arXiv) 2025 On Process
RM-PoT, a three-stage framework that integrates problem reformulation (RM), code-aided reasoning (PoT), and domain-aware few-shot learning to address these limitations. Our approach first reformulates the input problem into diverse surface forms to reduce structural bias, then retrieves five semantically aligned examples from a pre-constructed domain-specific question bank to provide contextual guidance, and finally generates executable Python code for precise computation.
2024
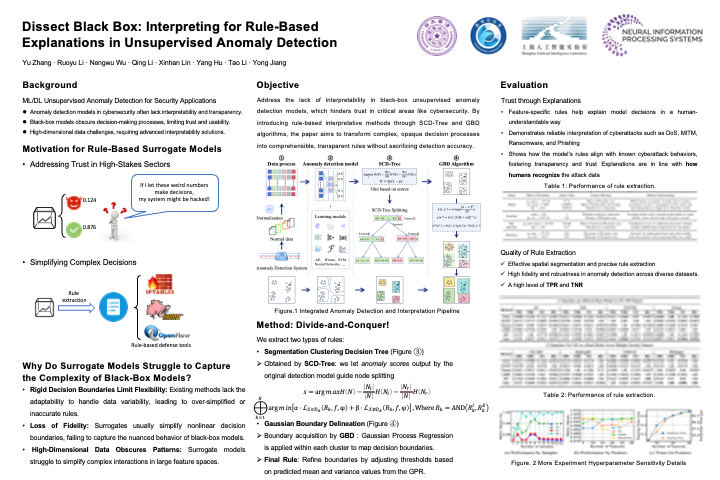
Dissect Black Box: Interpreting for Rule-Based Explanations in Unsupervised Anomaly Detection
Yu Zhang, Ruoyu Li, Nengwu Wu, Qing Li, Xinhan Lin, Yang Hu, Tao Li, Yong Jiang
(NeurIPS) 2024 NeurIPS
This paper introduces the Segmentation Clustering Decision Tree (SCD-Tree) for interpretable rule-based explanations in unsupervised anomaly detection. The SCD-Tree dissects black-box models by clustering normal data distributions, integrating anomaly detection insights to enhance segmentation. The Gaussian Boundary Delineation (GBD) algorithm then refines these clusters, distinguishing normal from anomalous data with resilience to data drift. This method transforms complex anomaly detection into interpretable rules, demonstrated to improve explanation accuracy and robustness across various datasets, which is crucial for high-stakes fields such as network and IoT security.
Dissect Black Box: Interpreting for Rule-Based Explanations in Unsupervised Anomaly Detection
Yu Zhang, Ruoyu Li, Nengwu Wu, Qing Li, Xinhan Lin, Yang Hu, Tao Li, Yong Jiang
(NeurIPS) 2024 NeurIPS
This paper introduces the Segmentation Clustering Decision Tree (SCD-Tree) for interpretable rule-based explanations in unsupervised anomaly detection. The SCD-Tree dissects black-box models by clustering normal data distributions, integrating anomaly detection insights to enhance segmentation. The Gaussian Boundary Delineation (GBD) algorithm then refines these clusters, distinguishing normal from anomalous data with resilience to data drift. This method transforms complex anomaly detection into interpretable rules, demonstrated to improve explanation accuracy and robustness across various datasets, which is crucial for high-stakes fields such as network and IoT security.

Genos: General In-Network Unsupervised Intrusion Detection by Rule Extraction
Ruoyu Li, Qing Li#, Yu Zhang, Dan Zhao, Xi Xiao, Yong Jiang (# corresponding author)
IEEE INFOCOM 2024 - IEEE Conference on Computer Communications 2024 IEEE INFOCOM
Genos is an unsupervised anomaly-based network intrusion detection framework utilizing programmable switches for high-throughput, in-network deployment. Unlike existing solutions, Genos leverages rule extraction for model-agnostic detection, featuring a Model Compiler, Model Interpreter, and Model Debugger to enhance interpretability and maintainability. Through a tree-based clustering and divide-and-conquer approach, Genos partitions feature space into subspaces for accurate boundary estimation and reduces updating overhead by selectively fine-tuning affected subspaces. Evaluation on physical hardware shows its capabilities of achieving 100 Gbps throughput, high interpretability, and minimal maintenance costs.
Genos: General In-Network Unsupervised Intrusion Detection by Rule Extraction
Ruoyu Li, Qing Li#, Yu Zhang, Dan Zhao, Xi Xiao, Yong Jiang (# corresponding author)
IEEE INFOCOM 2024 - IEEE Conference on Computer Communications 2024 IEEE INFOCOM
Genos is an unsupervised anomaly-based network intrusion detection framework utilizing programmable switches for high-throughput, in-network deployment. Unlike existing solutions, Genos leverages rule extraction for model-agnostic detection, featuring a Model Compiler, Model Interpreter, and Model Debugger to enhance interpretability and maintainability. Through a tree-based clustering and divide-and-conquer approach, Genos partitions feature space into subspaces for accurate boundary estimation and reduces updating overhead by selectively fine-tuning affected subspaces. Evaluation on physical hardware shows its capabilities of achieving 100 Gbps throughput, high interpretability, and minimal maintenance costs.
2023

Interpreting Unsupervised Anomaly Detection in Security via Rule Extraction
Ruoyu Li, Qing Li#, Yu Zhang, Dan Zhao, Yong Jiang, Yong Yang (# corresponding author)
(NeurIPS) 2023 NeurIPS
This paper introduces a post-hoc interpretability method for unsupervised anomaly detection in security by leveraging rule extraction. We propose distribution decomposition rules using an Interior Clustering Tree and Compositional Boundary Exploration (CBE) algorithm to decompose normal data distributions and approximate model decision boundaries. This approach provides interpretable explanations for anomaly detection models and allows the creation of a rule-based surrogate model for deployment. Experimental results across multiple datasets demonstrate that our method enhances model fidelity, correctness, and robustness, outperforming existing interpretability techniques in unsupervised anomaly detection.
Interpreting Unsupervised Anomaly Detection in Security via Rule Extraction
Ruoyu Li, Qing Li#, Yu Zhang, Dan Zhao, Yong Jiang, Yong Yang (# corresponding author)
(NeurIPS) 2023 NeurIPS
This paper introduces a post-hoc interpretability method for unsupervised anomaly detection in security by leveraging rule extraction. We propose distribution decomposition rules using an Interior Clustering Tree and Compositional Boundary Exploration (CBE) algorithm to decompose normal data distributions and approximate model decision boundaries. This approach provides interpretable explanations for anomaly detection models and allows the creation of a rule-based surrogate model for deployment. Experimental results across multiple datasets demonstrate that our method enhances model fidelity, correctness, and robustness, outperforming existing interpretability techniques in unsupervised anomaly detection.
2022

Deadline-Aware Dynamic Task Scheduling in Edge–Cloud Collaborative Computing
Yu Zhang, Bing Tang, Jincheng Luo, Jiaming Zhang
Electronics 2022
This paper explores a dynamic task scheduling approach in edge-cloud collaborative computing to meet the requirements of modern cyber-physical systems and Industrial IoT applications. The proposed scheduling algorithm, DSOTS, optimizes server selection and reduces latency in time-sensitive tasks. Further enhancement through a greedy strategy, TSGS, achieves server load balancing and minimizes SLA violations. Simulation results in an edge-cloud environment indicate that DSOTS reduces average processing time and cost by 30% and 45%, respectively, and SLA violations by 25% over current solutions.
Deadline-Aware Dynamic Task Scheduling in Edge–Cloud Collaborative Computing
Yu Zhang, Bing Tang, Jincheng Luo, Jiaming Zhang
Electronics 2022
This paper explores a dynamic task scheduling approach in edge-cloud collaborative computing to meet the requirements of modern cyber-physical systems and Industrial IoT applications. The proposed scheduling algorithm, DSOTS, optimizes server selection and reduces latency in time-sensitive tasks. Further enhancement through a greedy strategy, TSGS, achieves server load balancing and minimizes SLA violations. Simulation results in an edge-cloud environment indicate that DSOTS reduces average processing time and cost by 30% and 45%, respectively, and SLA violations by 25% over current solutions.